CISA Exam Pass Взлом 1.9 + Чит Коды
Разработчик: Yin Kai Leung Joseph
Категория: Образование
Цена: 499,00 ₽ (Скачать бесплатно)
Версия: 1.9
ID: j.cisa-exam
Скриншоты

Описание
Certified Information Systems Auditor, (CISA®)
________________________________________
This app is aiming to sit in on the exam. It mirrors the examination structure and covers the five CISA domains:
Domain 1: INFORMATION SYSTEMS AUDITING PROCESS- 21%
Domain 2: GOVERNANCE AND MANAGEMENT OF IT- 17%
Domain 3: INFORMATION SYSTEMS ACQUISITION, DEVELOPMENT AND IMPLEMENTATION- 12%
Domain 4: INFORMATION SYSTEMS OPERATIONS AND BUSINESS RESILIENCE- 23%
Domain 5: PROTECTION OF INFORMATION ASSETS- 27%
●Come with 2 mode of studying:
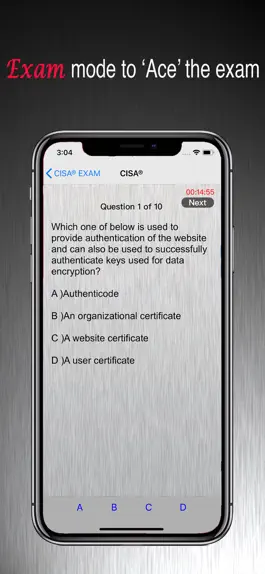
●Exam mode
●Practice mode
●Exam simulator consists of 3 modes:
● 4 hrs with 200 questions
● 30 mins with 20 questions
● 15 mins with 10 questions
●Including the missing exam study
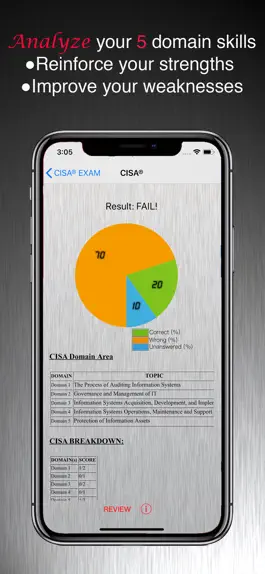
●Exam result assessment:
●Reinforce your strengths and,
●Improve your weaknesses
●Review mode to provide an intuitive interface to study
●Provide unlimited 'OFFLINE' access (24/7)
●Allow you to study on the go, anywhere and anytime (Without internet connection required)
_________________________________________________
WHO should download this app?
●If you're planning to appear for the CISA exam, and need to undergo a training that will help cover up the gaps in your knowledge.
●if you're someone wanting to get a broad-based view of the key aspects of information systems auditing
●if you're looking to build a career in auditing, and wish to get all your key concepts in place.
●Finally, you want to 'ACE' the exam
_________________________________________________
*We work hard to ensure 100% customer satisfaction. If you are having a problem with this product, you are welcome to contact us.
______________________________
Disclaimer
Information Systems Audit and Control Association does not endorse of otherwise sponsor this application and make no warranty, guarantee, or representation expressed or implied, as to its accuracy or content. CISA®, CISA and Certified Information Systems Auditor are trademarks or registered trademarks of Information Systems Audit and Control Association.
The content or information provided by this app is for reference only. NevsTops endeavors to ensure the accuracy of the information on this app. No warranty is given by NevsTops to the accuracy of the information. NevsTop shall not be liable for any loss or damages from the use of or inability to use this app, or any material contained in it, or from any action or decision taken as a result of using this app.
________________________________________
This app is aiming to sit in on the exam. It mirrors the examination structure and covers the five CISA domains:
Domain 1: INFORMATION SYSTEMS AUDITING PROCESS- 21%
Domain 2: GOVERNANCE AND MANAGEMENT OF IT- 17%
Domain 3: INFORMATION SYSTEMS ACQUISITION, DEVELOPMENT AND IMPLEMENTATION- 12%
Domain 4: INFORMATION SYSTEMS OPERATIONS AND BUSINESS RESILIENCE- 23%
Domain 5: PROTECTION OF INFORMATION ASSETS- 27%
●Come with 2 mode of studying:
●Exam mode
●Practice mode
●Exam simulator consists of 3 modes:
● 4 hrs with 200 questions
● 30 mins with 20 questions
● 15 mins with 10 questions
●Including the missing exam study
●Exam result assessment:
●Reinforce your strengths and,
●Improve your weaknesses
●Review mode to provide an intuitive interface to study
●Provide unlimited 'OFFLINE' access (24/7)
●Allow you to study on the go, anywhere and anytime (Without internet connection required)
_________________________________________________
WHO should download this app?
●If you're planning to appear for the CISA exam, and need to undergo a training that will help cover up the gaps in your knowledge.
●if you're someone wanting to get a broad-based view of the key aspects of information systems auditing
●if you're looking to build a career in auditing, and wish to get all your key concepts in place.
●Finally, you want to 'ACE' the exam
_________________________________________________
*We work hard to ensure 100% customer satisfaction. If you are having a problem with this product, you are welcome to contact us.
______________________________
Disclaimer
Information Systems Audit and Control Association does not endorse of otherwise sponsor this application and make no warranty, guarantee, or representation expressed or implied, as to its accuracy or content. CISA®, CISA and Certified Information Systems Auditor are trademarks or registered trademarks of Information Systems Audit and Control Association.
The content or information provided by this app is for reference only. NevsTops endeavors to ensure the accuracy of the information on this app. No warranty is given by NevsTops to the accuracy of the information. NevsTop shall not be liable for any loss or damages from the use of or inability to use this app, or any material contained in it, or from any action or decision taken as a result of using this app.
История обновлений
1.9
2021-06-15
-Questions updating
-Menu button added
-Menu button added
1.8
2021-05-18
Questions updating
1.6
2020-10-22
Domain Areas updated:
1.INFORMATION SYSTEMS AUDITING PROCESS
1.1. Planning
1.1.1. Introduction
1.1.2. IS Audit Standards, Guidelines, and Codes of Ethics
1.1.3. Business Processes and Audits
1.1.4. Types of Controls
1.1.5. Risk-Based Audit Planning
1.1.6. Types of Audits and Assessments
1.2. Execution
1.2.1. Audit Project Management
1.2.2. Sampling Methodology
1.2.3. Audit Evidence Collection Techniques
1.2.4. Data Analytics
1.2.5. Reporting and Communication Techniques
2.GOVERNANCE AND MANAGEMENT OF IT
2.1. IT Governance
2.1.1. IT Governance and IT Strategy
2.1.2. IT-Related Frameworks
2.1.3. IT Standards, Policies, Procedures and Guideline
2.1.4. Organizational Structure
2.1.5. Segregation of duties / separation of duties
2.1.6. Enterprise Architecture
2.1.7. Enterprise Risk Management
2.1.8. Maturity Models
2.1.9. Laws, Regulations, and Industry Standards affecting the Organization
2.2. IT Management
2.2.1. IT Resource Management
2.2.2. IT Service Provider Acquisition and Management
2.2.3. IT Performance Monitoring and Reporting
2.2.4. Quality Assurance and Quality Management of IT
3.INFORMATION SYSTEMS ACQUISITION, DEVELOPMENT AND IMPLEMENTATION
3.1. Information Systems Acquisition and Development
3.1.1. Project Governance and Management
3.1.2. Business Case and Feasibility Analysis
3.1.3. System Development Methodologies
3.1.4. Control Identification and Design
3.2. Information Systems Implementation
3.2.1. Testing Methodologies
3.2.2. Change, Configuration and Release Management
3.2.3. System Migration, Infrastructure Deployment, and Data Conversion
3.2.4. Post-implementation Review
4.INFORMATION SYSTEMS OPERATIONS AND BUSINESS RESILIENCE
4.1. Information Systems Operations
4.1.1. Common Technology Components
4.1.2. IT Asset Management
4.1.3. Job Scheduling and Production Process Automation
4.1.4. System Interfaces
4.1.5. End-User Computing (EUC)
4.1.6. Data Governance
4.1.7. Systems Performance Management
4.1.8. Problem and Incident Management
4.1.9. Change, Configuration, Release, and Patch Management
4.1.10. IT Service Level Management
4.1.11. Database Management
4.2. Business Resilience
4.2.1. Business Impact Analysis (BIA)
4.2.2. System Resiliency
4.2.3. Data Backup, Storage, and Restoration
4.2.4. Business Continuity Plan (BCP)
4.2.5. Disaster Recovery Plans (DRP)
5.PROTECTION OF INFORMATION ASSETS
5.1. Information Asset Security and Control
5.1.1. Introduction
5.1.2. Information Asset Security Frameworks, Standards, and Guidelines
5.1.3. Privacy Principles
5.1.4. Physical Access and Environmental Controls
5.1.5. Identity and Access Management
5.1.6. Network and End-Point Security
5.1.7. Data Classification
5.1.8. Data Encryption and Encryption-Related Techniques
5.1.9. Public Key Infrastructure (PKI)
5.1.10. Web-Based Communication Techniques
5.1.11. Virtualized Environments
5.1.12. Mobile, Wireless, and Internet-of-Things (IoT) Devices
5.2. Security Event Management
5.2.1. Security Awareness Training and Programs
5.2.2. Information System Attack Methods and Techniques
5.2.3. Security Testing Tools and Techniques
5.2.4. Security Monitoring Tools and Techniques
5.2.5. Incident Response Management
5.2.6. Evidence Collection and Forensics
1.INFORMATION SYSTEMS AUDITING PROCESS
1.1. Planning
1.1.1. Introduction
1.1.2. IS Audit Standards, Guidelines, and Codes of Ethics
1.1.3. Business Processes and Audits
1.1.4. Types of Controls
1.1.5. Risk-Based Audit Planning
1.1.6. Types of Audits and Assessments
1.2. Execution
1.2.1. Audit Project Management
1.2.2. Sampling Methodology
1.2.3. Audit Evidence Collection Techniques
1.2.4. Data Analytics
1.2.5. Reporting and Communication Techniques
2.GOVERNANCE AND MANAGEMENT OF IT
2.1. IT Governance
2.1.1. IT Governance and IT Strategy
2.1.2. IT-Related Frameworks
2.1.3. IT Standards, Policies, Procedures and Guideline
2.1.4. Organizational Structure
2.1.5. Segregation of duties / separation of duties
2.1.6. Enterprise Architecture
2.1.7. Enterprise Risk Management
2.1.8. Maturity Models
2.1.9. Laws, Regulations, and Industry Standards affecting the Organization
2.2. IT Management
2.2.1. IT Resource Management
2.2.2. IT Service Provider Acquisition and Management
2.2.3. IT Performance Monitoring and Reporting
2.2.4. Quality Assurance and Quality Management of IT
3.INFORMATION SYSTEMS ACQUISITION, DEVELOPMENT AND IMPLEMENTATION
3.1. Information Systems Acquisition and Development
3.1.1. Project Governance and Management
3.1.2. Business Case and Feasibility Analysis
3.1.3. System Development Methodologies
3.1.4. Control Identification and Design
3.2. Information Systems Implementation
3.2.1. Testing Methodologies
3.2.2. Change, Configuration and Release Management
3.2.3. System Migration, Infrastructure Deployment, and Data Conversion
3.2.4. Post-implementation Review
4.INFORMATION SYSTEMS OPERATIONS AND BUSINESS RESILIENCE
4.1. Information Systems Operations
4.1.1. Common Technology Components
4.1.2. IT Asset Management
4.1.3. Job Scheduling and Production Process Automation
4.1.4. System Interfaces
4.1.5. End-User Computing (EUC)
4.1.6. Data Governance
4.1.7. Systems Performance Management
4.1.8. Problem and Incident Management
4.1.9. Change, Configuration, Release, and Patch Management
4.1.10. IT Service Level Management
4.1.11. Database Management
4.2. Business Resilience
4.2.1. Business Impact Analysis (BIA)
4.2.2. System Resiliency
4.2.3. Data Backup, Storage, and Restoration
4.2.4. Business Continuity Plan (BCP)
4.2.5. Disaster Recovery Plans (DRP)
5.PROTECTION OF INFORMATION ASSETS
5.1. Information Asset Security and Control
5.1.1. Introduction
5.1.2. Information Asset Security Frameworks, Standards, and Guidelines
5.1.3. Privacy Principles
5.1.4. Physical Access and Environmental Controls
5.1.5. Identity and Access Management
5.1.6. Network and End-Point Security
5.1.7. Data Classification
5.1.8. Data Encryption and Encryption-Related Techniques
5.1.9. Public Key Infrastructure (PKI)
5.1.10. Web-Based Communication Techniques
5.1.11. Virtualized Environments
5.1.12. Mobile, Wireless, and Internet-of-Things (IoT) Devices
5.2. Security Event Management
5.2.1. Security Awareness Training and Programs
5.2.2. Information System Attack Methods and Techniques
5.2.3. Security Testing Tools and Techniques
5.2.4. Security Monitoring Tools and Techniques
5.2.5. Incident Response Management
5.2.6. Evidence Collection and Forensics
1.5
2018-09-15
CISA 26th Edition
1.4
2016-07-18
-Typo
-Alignment issues
-More up-to-date questions added
-Alignment issues
-More up-to-date questions added
1.1
2016-06-21
-more up-to-date questions
1.0
2016-03-09
Способы взлома CISA Exam Pass
- Промо коды и коды погашений (Получить коды)
Скачать взломанный APK файл
Скачать CISA Exam Pass MOD APK
Запросить взлом

